Hackers are getting smarter every day. It’s a very scary and very real thing. By going through the infrastructure which delivers web assets across the globe and intercepting a domain’s IP lookup, hackers are able to redirect Internet users to malicious IP addresses, getting exactly what they bargained for. The best thing we can do to prevent it is to get smarter as well.
This is where it comes in
A fairly new process, DNSSEC is a set of protocols adding a supplemental security layer to the domain name system, preventing hackers from getting what they want.
It’s an added level of online security, and it might be exactly what your online business needs. It is available with most online domain registrars, and you can read more of what is specifically offered if you click here.
So what is it?
It is simply a tool that assures Internet users won’t be redirected to fraudulent web addresses.
Being the set of security protocols that it is, it protects against forged and manipulated Domain Name System (DNS) data. Cyber attacks such as cache poisoning and pharming are especially prevalent, and DNSSEC combats this by matching cryptographic signatures to DNS records.
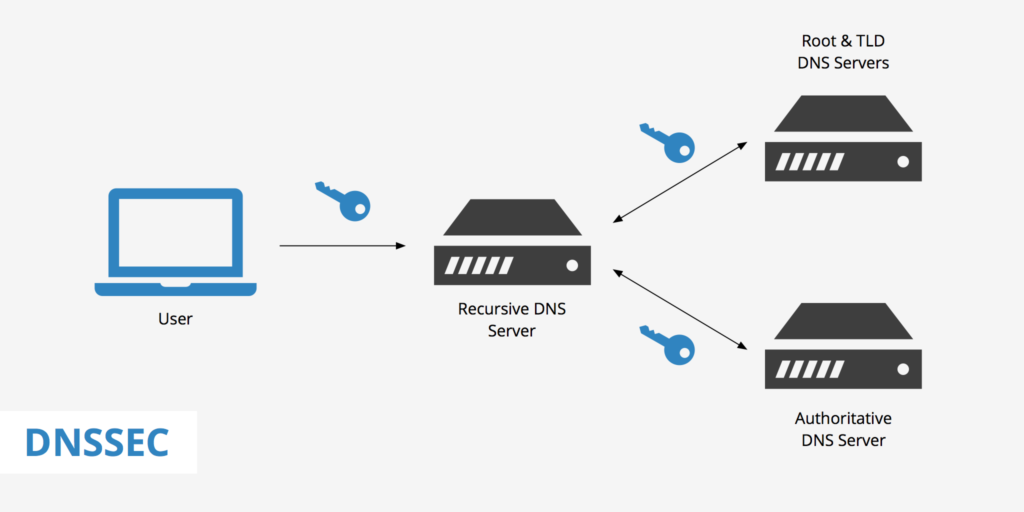
Cryptographic (or digital) signatures, maintained on the DNS server, are verified by a resolver. This resolver inspects the digital signatures embedded in the data when an Internet user enters a web address in their web browser. Data in the digital signatures must be identical to the data in DNS records for the connection to hit the ground running.
Also, it makes it increasingly difficult for traditional DNS records to be forged and/or modified.
Is DNSSEC and DNS the Same Thing?
You might be confused about how DNS works into this scenario. I’ll show you.
DNS is merely a means of translating domain names into numeric IP addresses. It makes it easier for an Internet user to remember words instead of numbers after all. But there’s a catch: it’s easy for security breaches to occur.
Traditionally, the DNS system uses unencrypted data for its records.
That’s why DNSSEC is helpful in this situation. It’s an extension to DNS, filling in the gaps, and combating any security vulnerabilities.
And so, DNSSEC and DNS complement each other, working hand-in-hand.
How Does It Work?

DNSSEC digitally signs records for DNS lookup using public key cryptography. Additionally, it verifies an Internet user is reaching a designated website with nothing shady in between.
By a chain of trust, the correct DNSKEY record is authenticated and validated. The digital signature is analyzed so that the DNS resolver is able to confirm the information is identical to the information published by the zone owner.
This information published by a zone owner must be on an authoritative DNS server. Curious as to what DNSKEY is? It simply holds public signing keys, and it’s one of the many new records added to DNS settings. Other new records include RRSIG, DS, NSEC and NSEC3, and CDNSKEY and CDS.
All of these records are accessed the same as any DNS record would be, but these are also different for the fact that they’re used to digitally sign a domain.
Equally important, DNSSEC functions with two main types of keys: zone-signing keys (ZSKs) and key-signing keys (KSKs). The first, ZSKs, hold a public and private key portion which is used to validate designated record sets within a Zone. KSKs merely sign DNSKEY records.
Once the information is identical and validated, you’re good to go! And that’s that.
Why is it Important/how Will it Affect Your Business?
Do hackers make you nervous? Then having an extra level of security implemented onto your website is a good idea.
There’s a very high chance you’re already exposed to DNS attacks if you’re only running under a standard DNS server without any form of DNS record validation. When that’s the case, it’s extremely easy for a hacker to redirect your DNS records to wherever they’d like.
DNSSEC protects against a plethora of cyber attacks. Like I mentioned previously, it protects against cache poisoning and pharming but also DNS spoofing and MITM attacks. Without it, DNS hijacking and DNS spoofing are especially prevalent occurrences.
Additionally, DNSSEC creates an added sense of trust and confidence in online activities used for any online business. This includes e-commerce and VoIP.
Under a DNS attack, there’s high potential for losing your business’s customers and its SEO rankings (these are vital if you want to stay open for business!) With DNSSEC, you won’t have to worry.
So How do I Get on Board?
Nothing good ever came easy.
The process of enabling it is not so straight-forward, but what’s worth attaining is worth fighting for.
As necessary as DNSSEC should be across all platforms and for all online businesses, many registrars don’t yet support this technology for their domain names. Likewise, some registrars don’t support all TLDs, another issue making it difficult to activate it in the first place.
To commence with it, a registrar must (obviously) have this form of validation technology available within their domain name infrastructure as well as the DNS server.
Thankfully, ICANN makes it easier for you. On their website, they maintain an updated list of domain registrars who do, in fact, support it and the supported TLDs.
Summary

DNSSEC is a strong, new development for protecting your domain names and DNS security.
With DNSSEC, your information is secured against hackers and cyber attacks. It encrypts data which only enabled DNS servers have access to.
That being said, adoption is exceedingly slow across all platforms and online businesses as DNSSEC deployment is in an early stage. Moreover, true domain security across all major registrars is years in the making.
On the other hand, DNSSEC deployment is on the rise as more and more people learn about it and the advantages of it. Hopefully, adoption rates of it will rise in response to the epidemic of security breaches across the Internet’s infrastructure today.
DNSSEC works for you, assuring you and your customers a sense of trust and confidence in knowing your personal information is safeguarded in the DNS lookup process.
Now that you know about it and all the risks that could happen if you manage without it, why wait?





