I think most of the people in this world understand just how important social media platforms have become. This new way of communicating with each other and sharing information is truly remarkable. It does not matter whether you are in Russia or on the other side of the planet in the United States. With access to the Internet and social media websites, our new ability to communicate is simply amazing.
But, the real interesting thing about this new form of communication is that it is not just about making a connection between two individuals. Companies can utilize it to boost brand recognition and to increase profits. These platforms allow businesses to share their services or products to potential customers in a very effective way.
However, like any other website on this world, social media platforms do have both pros and cons. The pros of utilizing this for your business are quite obvious. The cons on the other hand are not as obvious and can cause serious damage.
As a business owner, you probably understand just how important social media is to push your new products and services. You cannot afford not to use this form of marketing. This is why you must understand all of the risks that come with advertising and communicating with your client through sites such as Facebook, Instagram, or Twitter.
Once you start understanding those risks, you can start managing them effectively. To help you with that, this article will focus on those exact risks.

Is your account safe?
A lot of people and businesses believe that their Facebook or Instagram account is safe because there hasn’t been any weird activity on it. While this is a legitimate way of ensuring that your account is safe and out of the hands of hackers or competitors, it is not enough for a business. You will need to take every step to ensure that your employees are the only people who have access to your profile.
This is especially vital because hacking profiles has become a much more common occurrence on any of these social media websites. Sometimes, it doesn’t even require a hack for someone to get access to your company’s profile. For example, there have been several worldwide leaks for sites such as Facebook or Instagram. These security loopholes have been fixed by said sites, but the damage has already been done. Who knows whether your business’s information has been leaked or not?
So, the best way to manage this risk is to perform frequent checks on the login situation of your account. Both Facebook and Instagram allow you to analyze which devices have been used for signing in and the information about their location too. If you see any kind of weird activity, make sure you change all of your login information. That means your email, your password, and the security questions.
Be wary with whom you are sharing login information
One of the easiest ways someone can get access to your account and use it to their benefit or cause problems to your company is by directly giving them access.
I know, this doesn’t seem like something that happens often, but it actually does. One of the most common ways people steal passwords is through fake administration emails. It is important to understand that a company’s customer support will never ask for any kind of access information. So, if you ever get an email from Facebook or Instagram asking you for your password, make sure you never respond to that email.
You should also be wary about sharing your password with your employees. Of course, those that are very close to you and if there is a lot of trust between you two, you probably shouldn’t worry about any issues in the future. However, I would suggest that you avoid sharing passwords with new and unreliable employees.
Assuming that you do not feel comfortable sharing your company’s social media account with any of your employees, but you still need help managing it, there are tons of applications out there that will help you with that exact problem. If you click here, you can see just how much applications such as Hootsuite and Kontentino can help you manage your social media.
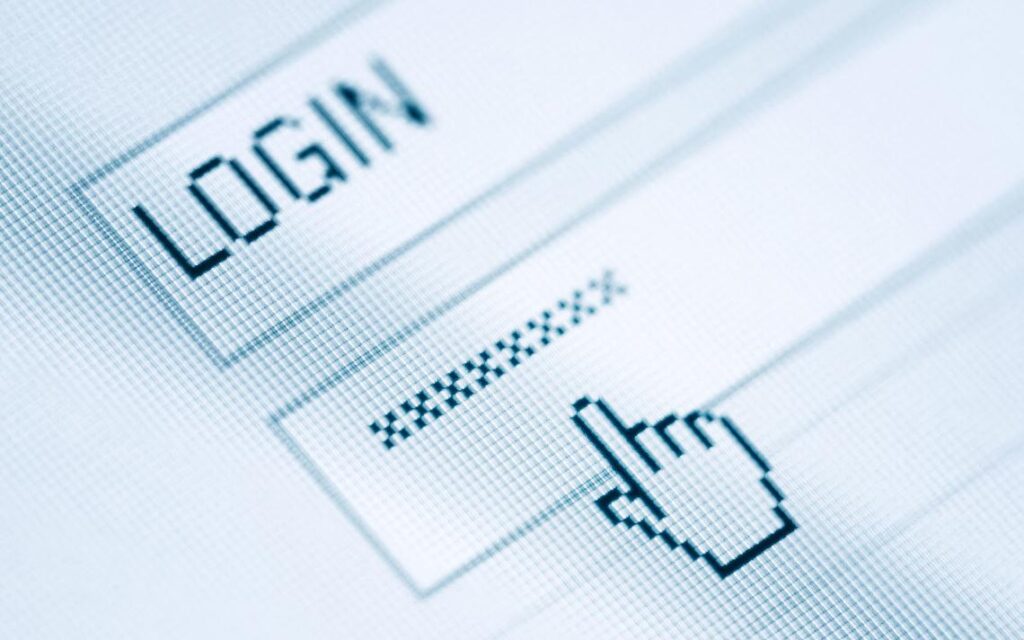
Good password etiquette
Believe it or not, but many times the accounts get hacked by people guessing the passwords. I know, it sounds impossible. How would someone guess a word, a number, or a series of letters and letters randomly? Well, experienced crackers don’t just mash random values into their keyword. They have these advanced programs that can input thousands of words in a matter of minutes.
This is why having a good password etiquette is vital for security. By using common and simple words such as apple, door, your company’s name, or anything similar to these examples, you are effectively increasing your chances of getting hacked. If you feel like you have to use a simple word that you can remember, at least add random numbers and special symbols to it.
By adding a number or a symbol at the beginning or at the end of the word, you will decrease the chances of getting hacked considerably. In fact, those advanced programs that I mentioned can’t crack passwords that have random numbers and symbols in it. This is probably the reason why many websites require you to add a number or symbol in your password when creating an account.
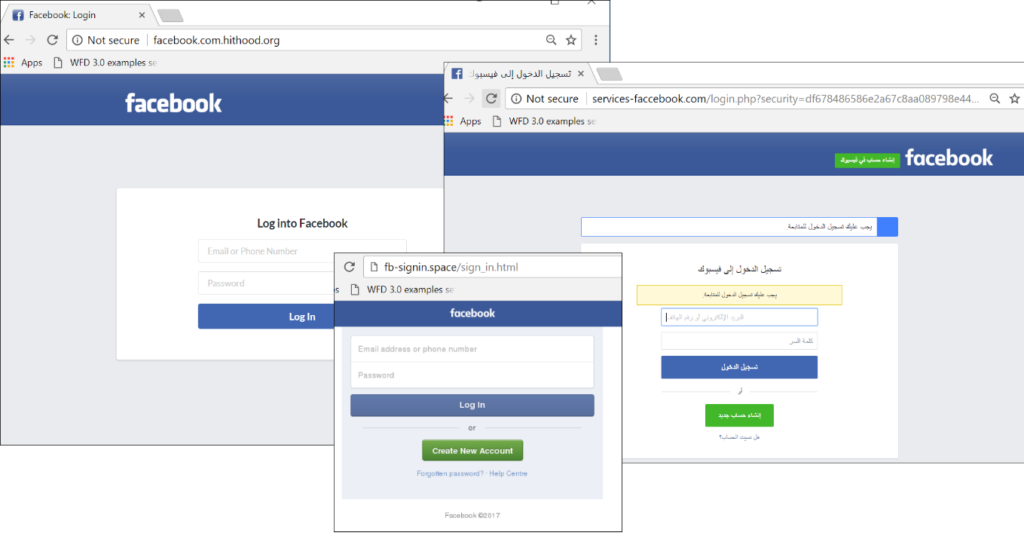
Phishing sites
Another effective way hackers used to steal information is through phishing sites. The way these sites work is pretty basic. They copy the look of certain websites, let’s say Facebook, and use a domain name that is similar to Facebook’s domain name. For example, they could use something like Face.book.com. It seems obvious when looking at it this way, but when you are surfing on the Internet, you probably wouldn’t have noticed it.
It is vital that you are wary about where you are inputting your private information.
By following the steps we mentioned in this article, I believe that you will be able to manage social radio masks much more effectively.